[Forensics] Why your Mac (sort of) keeps a record of every file you've ever downloaded from the internet
Investigating the Quarantine Events V2 database
Your Mac (sort of) keeps a record of every file you’ve downloaded from the internet.
It’s stored in a SQLite database called Quarantine Events V2 (located at ~/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV2).
But why is macOS collecting all this information in the first place?
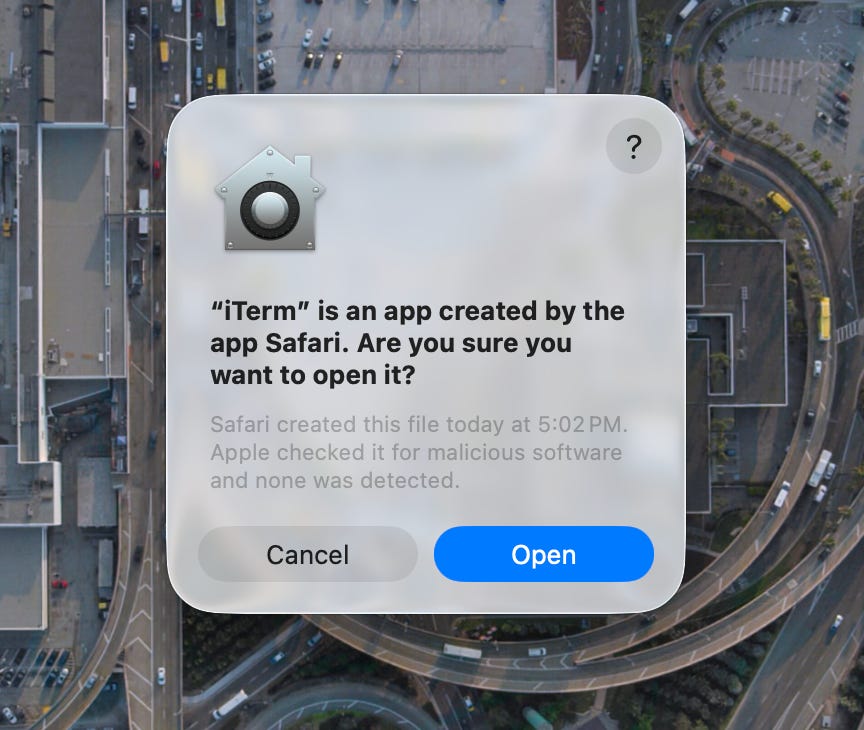
Mac uses this database to warn users before opening potentially malicious files downloaded from the internet. It’s the feature that gives you the notifications asking: “[downloaded app] is an app created by the app [source app]. Are you sure you want to open it?”
macOS has had a quarantine system since Leopard (10.5). Gatekeeper, the built-in security feature that verifies that a downloaded app is from an identified developer (code signing) and has been submitted to Apple for malware scanning (notarization), builds on top of this quarantine system. When a quarantine-aware app like Safari, Chrome, or Mail downloads a file, macOS stamps it with a com.apple.quarantine attribute and logs the event in the QuarantineEventsV2 database.
The database schema includes: a UUID, timestamp, agent name (downloading application), bundle identifier, download URL, origin URL (the referring page), sender name/address (for email attachments), and a type number.
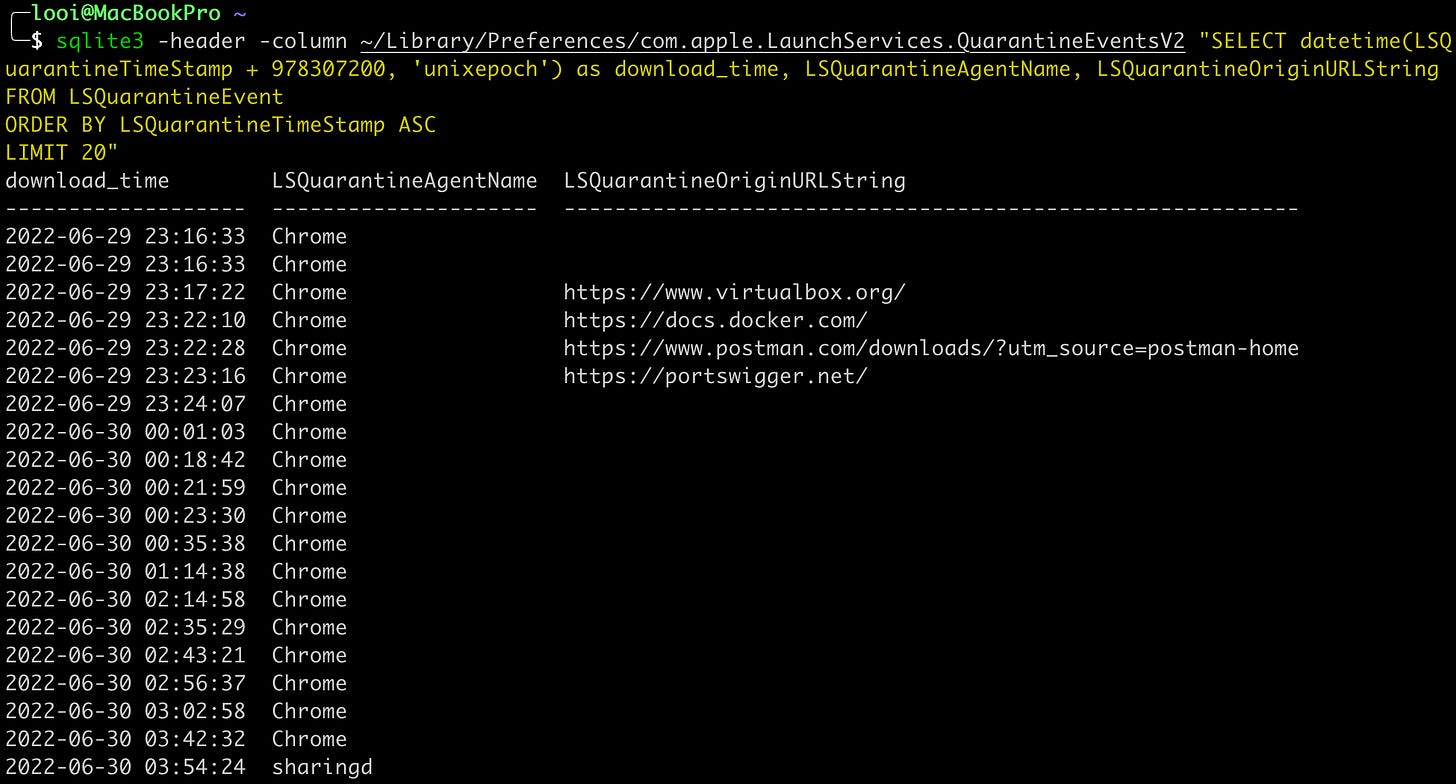
Notably absent is the actual filename. There is no column for it. The UUID ties to the extended attribute on the file, but once the file is deleted, that link is broken. You cannot recover the filename from this database alone. In practice, many fields are frequently empty. I queried my own Mac and reliably got timestamps and agent names. Origin URLs were populated for some entries, absent for others. Sender fields were almost never populated. Also, keep in mind that timestamps use Cocoa epoch (seconds since Jan 1, 2001). Add 978307200 to convert to Unix epoch.
So what is QuarantineEventsV2 actually good for?
Corroboration. Cross-reference quarantine timestamps with browser history, FSEvents, or Unified Logs to build a more complete timeline.
Agent name analysis. LSQuarantineAgentName reliably identifies the downloading application. AirDrop transfers show up as sharingd.
Persistence. macOS never cleans this database, even after files are deleted, Trash is emptied, and browser history is cleared.
Since this is just a SQLite database, you don’t need a custom parser! And for forensic workflows at scale, Velociraptor’s MacOS.System.QuarantineEvents artifact and Plaso’s ls_quarantine plugin already handle the parsing and timestamp conversion.
Try this on your own Mac:
sqlite3 -header -column ~/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV2 “SELECT datetime(LSQuarantineTimeStamp + 978307200, ‘unixepoch’) as download_time, LSQuarantineAgentName, LSQuarantineDataURLString FROM LSQuarantineEvent ORDER BY LSQuarantineTimeStamp DESC LIMIT 20"